What is PPTP (Point-To-Point Tunneling Protocol)?
date
Nov 15, 2022
slug
what-is-pptp
status
Published
summary
PPTP refers to Point to Point Tunneling Protocol that creates a connection between two computers through a secure tunnel. Learn the other details about PPTP and how it works.
tags
Website
type
Post
Author
Berktug Mutlu
category
Privacy & Security
meta_title
What is PPTP (Point-To-Point Tunneling Protocol)? Learn How It Works - FastVPN
Going back a few decades, the world of network security was a bit different. Back in those days, you didn’t have cyberattacks spilling out of every corner of the internet. Regardless, having a secure connection was made possible by PPTP.
Below, we will go through a complete review of the old protocol and let you know whether it is worth pursuing today.
What Is PPTP?History of PPTPHow PPTP WorksIs PPTP Fast?Is PPTP Secure?More Technical Aspects of PPTPIs PPTP Still Being Used?Alternatives to PPTPPPTP FAQsDo You Need a PPTP Client?What Tunneling Types are on PPTP?Conclusion – Is PPTP Worth It?
What Is PPTP?
PPTP, or Point-To-Point Tunneling Protocol), is a network protocol that connects two computers through a secure tunnel. It is the oldest known VPN protocol, popular with companies like Microsoft during the 1990s.
The protocol is obsolete by today’s standards but does come in native forms on several Windows platforms. The latest operating systems (Windows 11, 10, 7, and Vista) are part of this, with Windows Server releases up to 2012.
PPTP was specific for use with TCP/IP networks. Any other protocols conflicted with this protocol, making it a picky solution for remote access.
Microsoft used PPP (point to point protocol) flames to encrypt and compress data sent between multiple areas. PPP is the encryption part of the tunneling protocol that has seen no significant updates.
Unlike modern forms of VPN security, PPTP has weaker protection. The most up-to-dave version is v2, which uses 128- bit encryption keys. The most common use of the old protocol is between inter-network desktops and appliances.
History of PPTP
PPTP was in development during the mid to late 80s. The protocol was developed under Cisco, but a 1999 deployment was through Microsoft, Ascend Communications, and 3Com. Microsoft first introduced it with the NT 4.0 beta release.
The protocol saw an update in 2003 with Windows Server 2003. During the 2003 release, the protocol enhanced security to 128-bit encryption.
The old protocol mainly remained unchanged until after the release of Windows Server 2012. After 2013, Microsoft removed the protocol from the platform due to security concerns.
Today, it exists on all current Windows platforms but is not a central feature of the operating systems. You can also find it on the latest releases of Android (Android 12). There is no PPTP available on iOS or macOS devices.
How PPTP Works
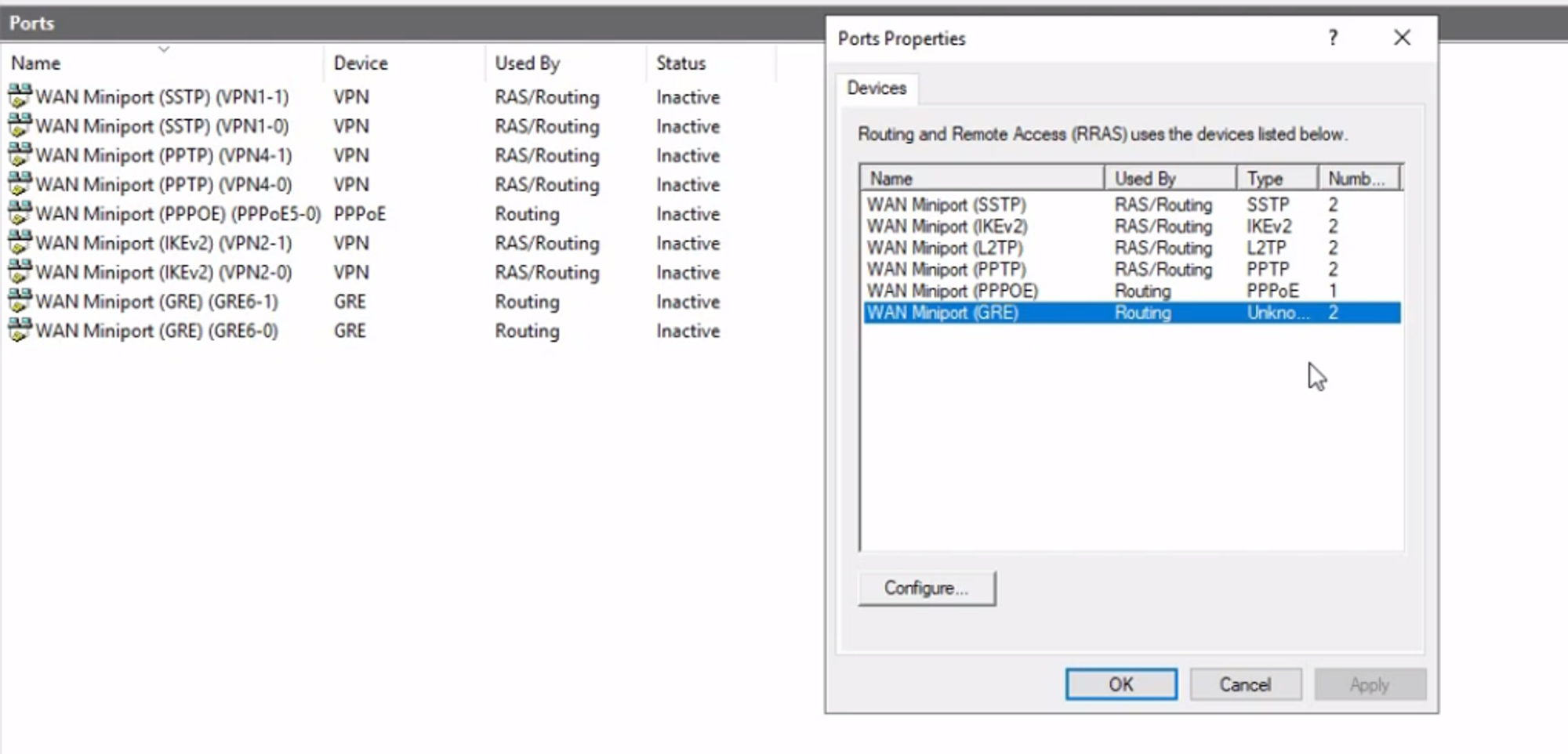
PPTP starts by creating a TCP connection using the open server port: 1723. The connection is encrypted using PPP, which gets repackaged using GRE (Generic Routing Encapsulation).
GRE is another tunneling protocol developed by Cisco. It is specific to IP connections, making it an alternative to IPSec (which does not work with this connection form). When used alongside it, you can create a VPN.
The connection establishes by sending data packets. The packets are encrypted using MPPE (Microsoft Point-to-Point Encryption), a part of the PPP. The encryption uses an RC4 (Rivest Cipher 4), a cipher popularized in the late 1980s by Ron Rivest.
Ciphers are algorithms used to encrypt and decrypt data. These algorithms programmatically transform data into gibberish so prying eyes cannot see what you send. Both ends of the connection use the cipher to encrypt before sending and decrypt as they receive it.
During this process, the receiving user needs to authenticate their identity. Authentication is the process of proving your identity using network credentials (such as a username and password).
MS-CHAP, or the Challenge Handshake Authentication Protocol, is commonly used to do this. It was the authentication protocol for use under Windows 95 and Windows 98.
In later forms of the protocol, you can use EAS-TLP as an alternative to MS-CHAP v2. EAS-TLP was s a popular choice due to higher security standards in 2003.
Is PPTP Fast?
PPTP is a lightweight VPN protocol due to its simplicity. This light code makes for excellent performance, regardless of how old your system is. So yes, it is fast.
Is PPTP Secure?
PPTP is not a safe choice for encrypting sensitive data. In 2012, Microsoft confirmed this by announcing its recognition of an exploit code for the protocol. They recommended that VPN solutions relying on MS-CHAP v2 and the tunneling protocol were insecure during the announcement.
Microsoft shared this after security researchers released tools during Defcon 2012 that could crack PPTP in under a day. In the following year, hackers also broke the famous RC4 cipher, part of the old protocol.
Hackers cracked the RC4 cipher in 2013, causing numerous web admins to try and replace the code. The code still had widespread use as a TLS/SSL connections component. Thankfully, the much more powerful 256-AES encryption was already available.
So the use of this old protocol does expose you to malicious attacks. Instead, focus on VPNs that use advanced technology.
More Technical Aspects of PPTP

While this protcol might have been viable in the late 90s and early 2000s, it had restrictions—namely, the requirement of direct connections.
PPTP does not have support for NAT devices. NAT devices are your gateway to the internet; a router is the most common form of device. So you need to do one of two things:
- You need a connection between two devices on a network that doesn’t go through a NAT device
- PPTP Passthrough allowance
PPTP Passthrough is a feature of specific routers that allow these unique VPNs to sidestep NAT requirements. This router requirement comes with Enhanced GRE and Call-ID.
A Call ID is a unique identifier (or header) that labels a PPTP connection. This header identifies the packet from a PPTP VPN when data is encrypted. Routers use this header to determine when to switch ports for a PPTP VPN’s unique needs.
Is PPTP Still Being Used?
It is still on multiple modern operating systems despite the numerous security flaws. Some older businesses also use the protocol for inter-office communication. However, those businesses should not rely on this protocol for sensitive data.
Still, it works to encrypt as a remote access client in a pinch. Just don’t rely on it outside of absolute necessities.
Alternatives to PPTP
Since the 1999 release of PPTP, numerous VPN protocols have come out. Here are a few alternatives to PPTP:
L2TP & IPSec
OpenVPN
IKEv2 & IPSec
Wireguard
SoftEther
SSTP
PPTP FAQs
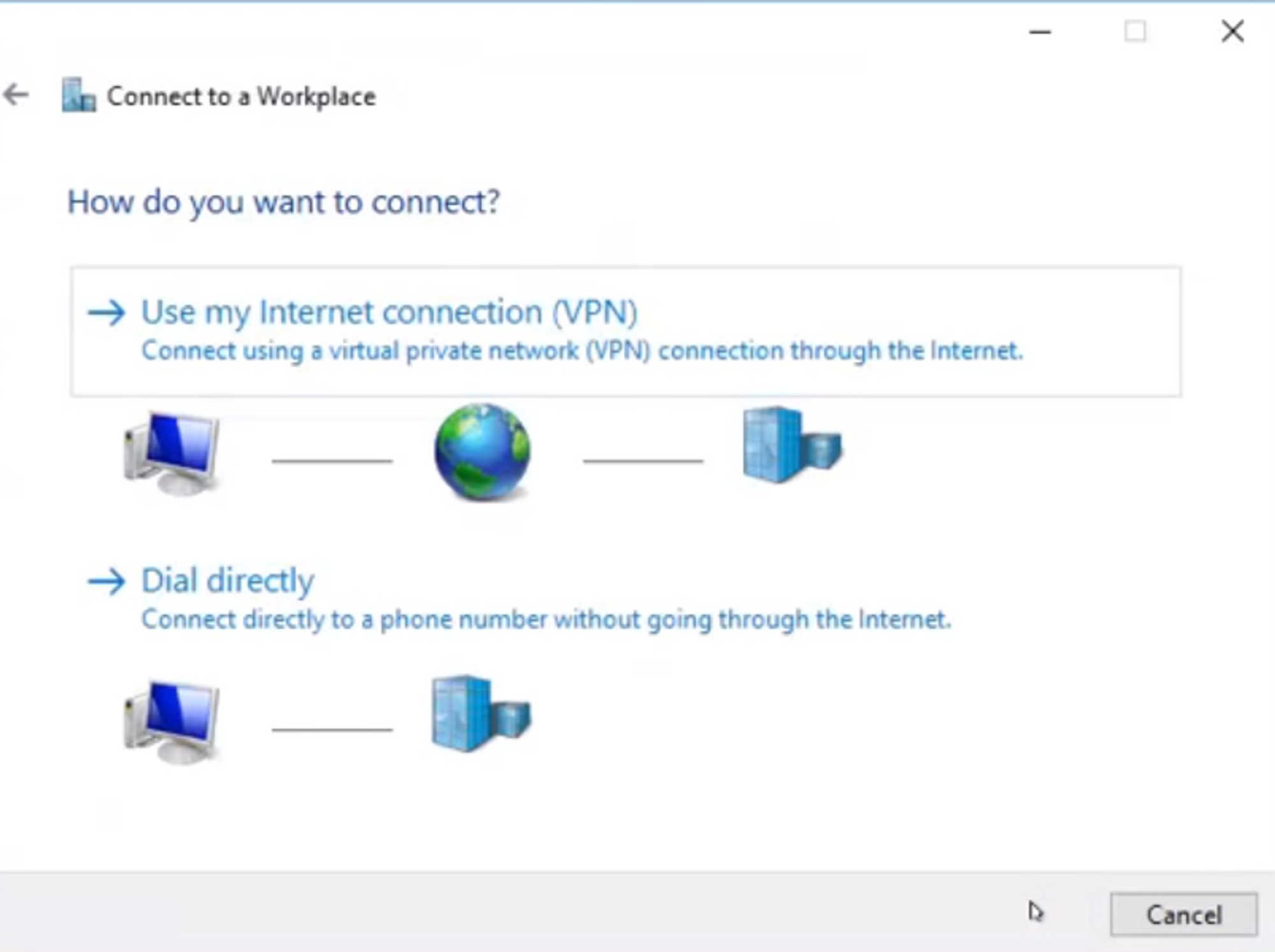
Do You Need a PPTP Client?
Unless you operate Apple devices, PPTP comes as a built-on client on most operating systems. Apple removed PPTP in favor of more robust protocols years ago, so you need a PPTP client on iOS or macOS.
What Tunneling Types are on PPTP?
There are two types of tunneling on PPTP. The PPTP server initiates compulsory tunneling from the ISP, while voluntary tunneling comes from an existing client’s request on a server.
Compulsory tunneling is less common because it is an old-fashioned remote access request. Internet Service Providers used to need it to troubleshoot issues on your network.
Conclusion – Is PPTP Worth It?
PPTP is obsolete because it is no longer secure. Despite how fast it is, the old-fashioned cipher and PPP were cracked years ago. Using it is to protect your personal data is asking for trouble.
For better security, The Fast VPN offers military-grade encryption. There are no leaks, ensuring much better security than PPTP. Download it today to ensure your online privacy.