How to Clear Cookies on Chrome, Firefox, Opera, and Other Browsers
date
Mar 7, 2022
slug
how-to-clear-cookies
status
Published
summary
Unlike an actual cookie’s delicious and soft enjoyableness, online cookies are a bit bland. Trying to eat them would be an act of insanity. Regardless, they are helpful for a small handful of reasons.
tags
Website
type
Post
Author
Berktug Mutlu
category
Personal Information
meta_title
How to Clear Cookies on Chrome, Firefox, Opera, and Other Browsers -FastVPN
Unlike an actual cookie’s delicious and soft enjoyableness, online cookies are a bit bland. Trying to eat them would be an act of insanity. Regardless, they are helpful for a small handful of reasons.
If internet privacy is your thing, it’s best to get them off your computer. Below, we will provide you with the ultimate guide to clearing cookies on any browser and operating system.
What are Cookies? (The Computer Kind)How To Clear Chrome’s CacheDesktop (Linux, Mac, and Windows)Mobile (Android and iOS)How To Clear Cookies on All Chromium-Based BrowsersHow to Delete Cookies on FirefoxDesktop (Windows, Mac, and Linux)Mobile (iOS and Android)How To Clear Cookies on OperaDesktop (Windows, Mac, ChromeOS, and Linux)Mobile (Android and iOS)Clearing Cookies on Microsoft EdgeDesktop (Windows, Mac, and Linux)Mobile (Android and iOS)Clearing Cache on SafariDesktopMobileDeleting Cookies on Internet ExplorerWhy Clear Cache and Cookies?Will Cookies Affect My VPN?Conclusion – How Important is Removing Cookies?What is Port Forwarding?Is Port Forwarding Safe?How to Port Forward on Your RouterStep One: Access Your Router’s Admin PageStep Two: Getting To The Port Forwarding PageStep Three: Finding The Port NumbersWhat if The Port Gives Me an Error?Does Port Forwarding Work With a VPN?Can You Port Forward on VPN Routers?Where Do You Use Port Forwarding?Virtual DesktopsGame ServersRemote Access and BackupsCCTV and SecurityTypes of Port ForwardingLocal Port ForwardingRemote Port ForwardingDynamic Port ForwardingPort Forwarding BenefitsPort Forwarding RisksPort Forwarding FAQsWhat is TCP?What is UDP?What is NAT?Conclusion – Should I Trust Port Forwarding?
What are Cookies? (The Computer Kind)
Before we get too far into the clearing party, it’s best to know what you are clearing. Cookies contain small bits of data about your visitation of a website:
- Who you are (based on a randomly generated number)
- Your site preferences
- Where you are from
Cookies don’t have too much data on you. But the existence of cookies can change your web experience. Those who emphasize privacy will want to remove them after every session.
There are also two types of cookies:
- First-party cookies store random numbers and site preferences. They also usually have expiration dates when the login you have to their site is no longer valid, requiring you to re-enter your username and password.
- Third-party cookies are set by sites you aren’t currently visiting but have elements on the site you are now on. For example, having a share button for Facebook will leave a third-party cookie.
Cookies (usually) make your web experience better. This is because having cached images and browser data prevents you from loading the entire page. You’ve already got the page pre-loaded on your system, saving you time.
Regardless, tracking cookies store information on you, which isn’t something smiled upon by privacy-conscious individuals.
How To Clear Chrome’s Cache
Chrome, Google’s browser, is known for gathering a lot of personal data. They work across all major operating systems and have a relatively straightforward process for clearing data.
Desktop (Linux, Mac, and Windows)
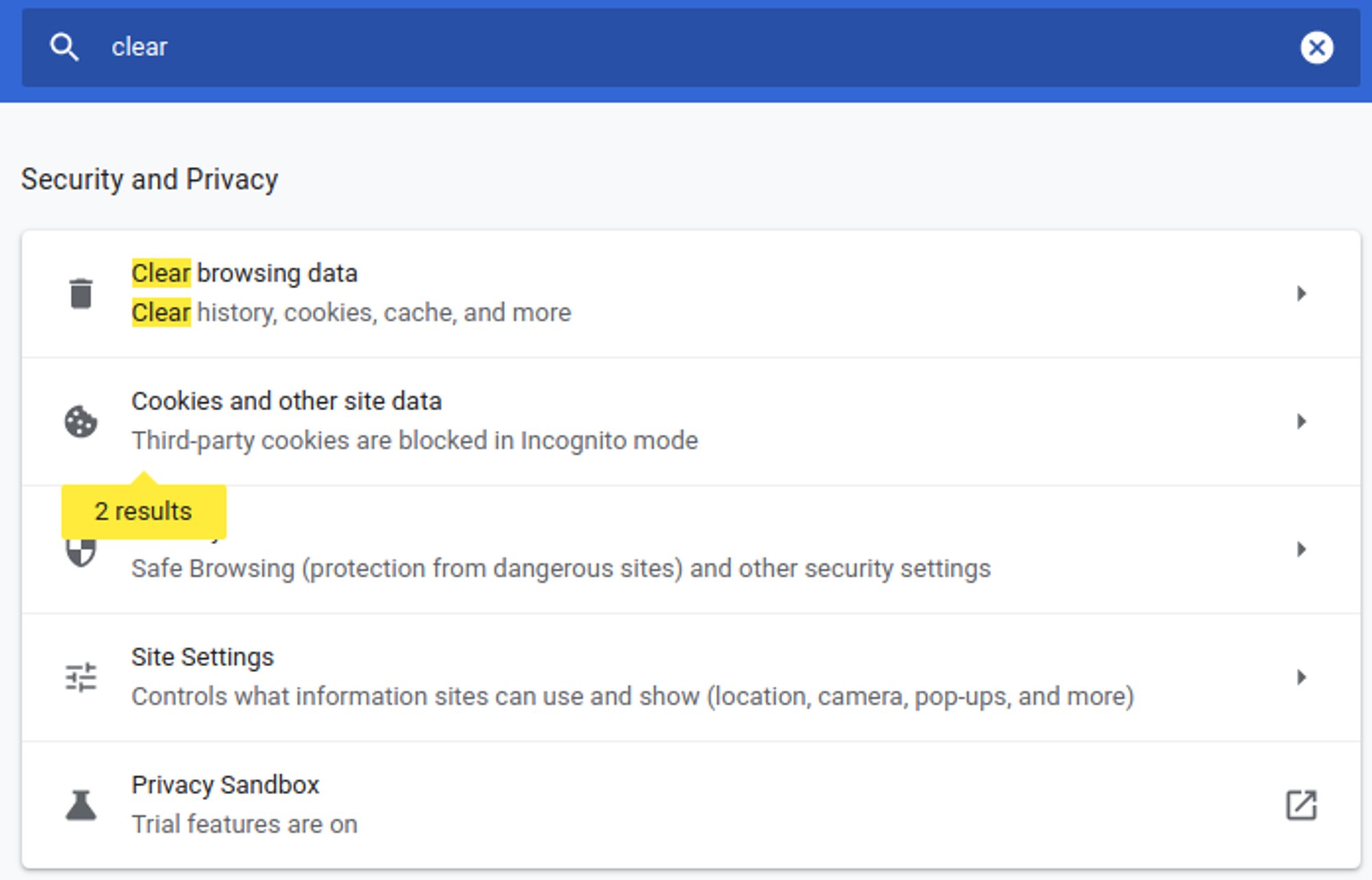
- Access Chrome’s settings in the upper-right hand corner by clicking the three dots
- Click settings and type “clear” in the search bar
- Click the first option that says “Clear browsing data.”
- Under “time range,” select all time if this is the first time you’ve done it in a while.
The advanced options on the right allow for a deeper clean. The deeper clean is excellent if you plan on moving your information away from Google. You can remove the following with advanced options:
- Sign-in data
- Autofill form data
- Site settings
- Hosted app data
Your basic settings will clear browsing history, cookies, and cached files.
Mobile (Android and iOS)
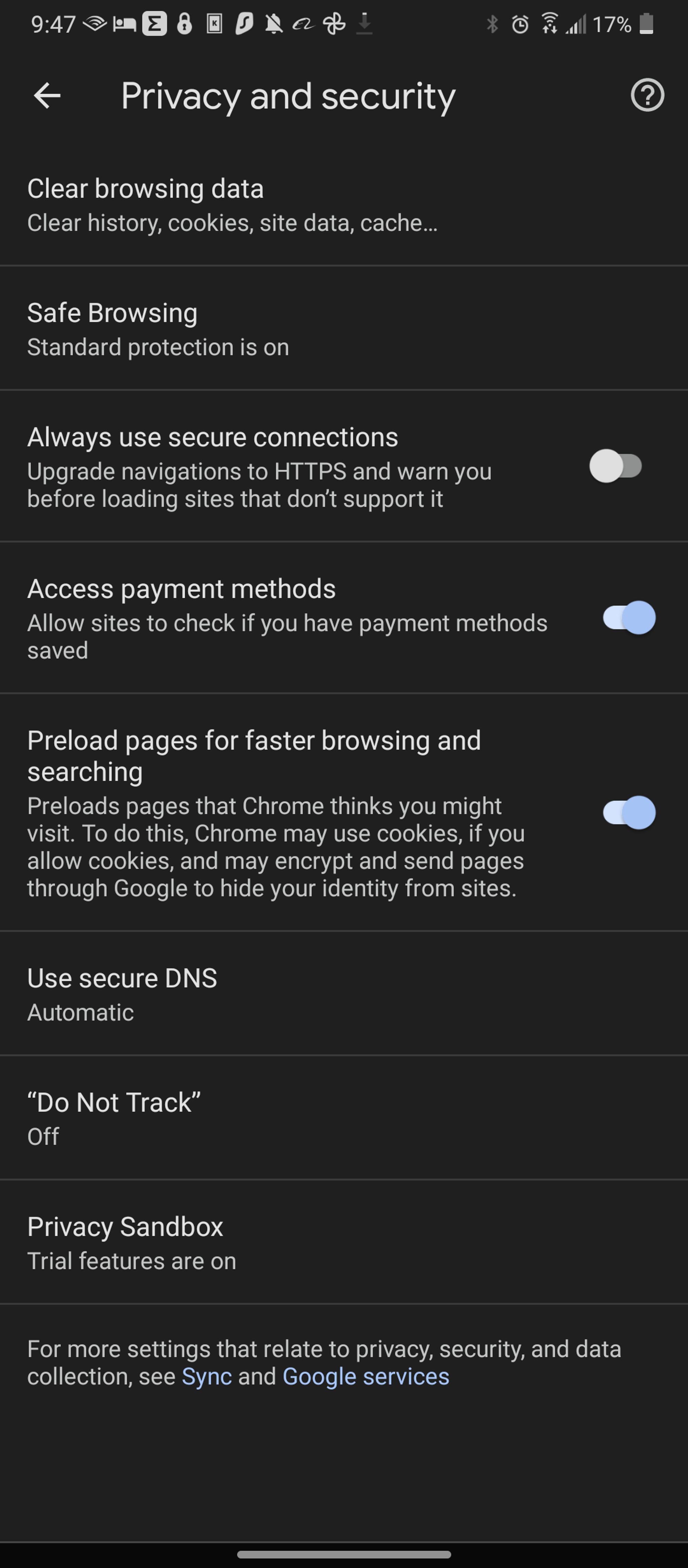
There is no search function available on mobile chrome browsers. Follow these steps to get around these limitations:
- Select settings from the three dots in the upper-right-hand corner.
- Scroll until you find “Privacy and security.”
- Tap “Clear browsing data.”
If Chrome is your regular, you can also take the opportunity to block all third-party and first-party cookies under general settings. You can also request always clear cookies when windows are closed for extra security.
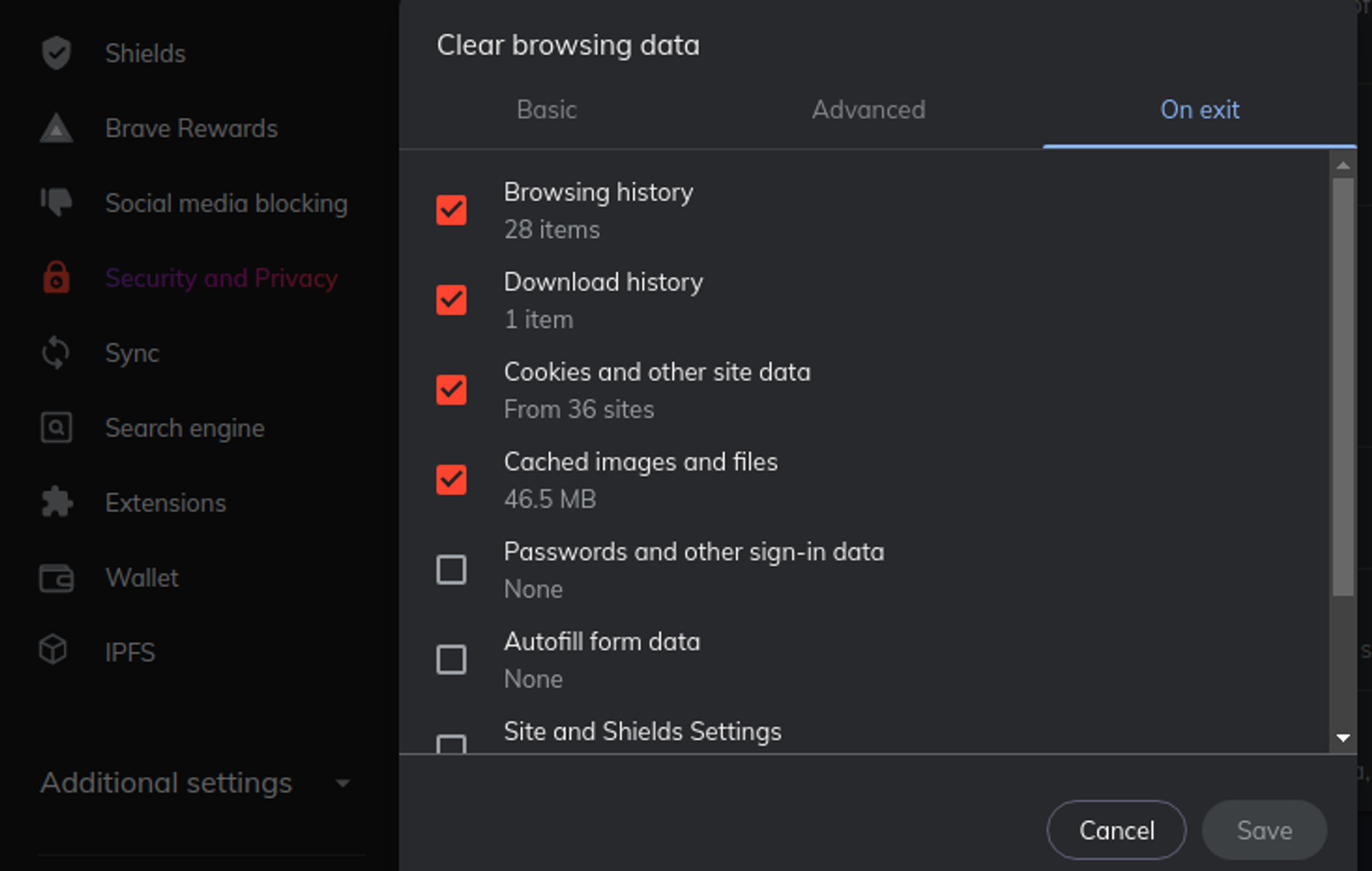
How To Clear Cookies on All Chromium-Based Browsers
There are a wide variety of Chromium-based browsers in the best browsers blog. You’ll find that many Chromium browsers have the same general steps. After all, they come from Google’s code.
Brave, a well-known privacy browser, follows the same process. The difference is that their selection to clear data is under the “clear browsing data” section under Security and Privacy.
How to Delete Cookies on Firefox
You will notice that clearing browsing data is pretty similar among these platforms. Firefox requires a few fewer clicks to get this done.
Desktop (Windows, Mac, and Linux)
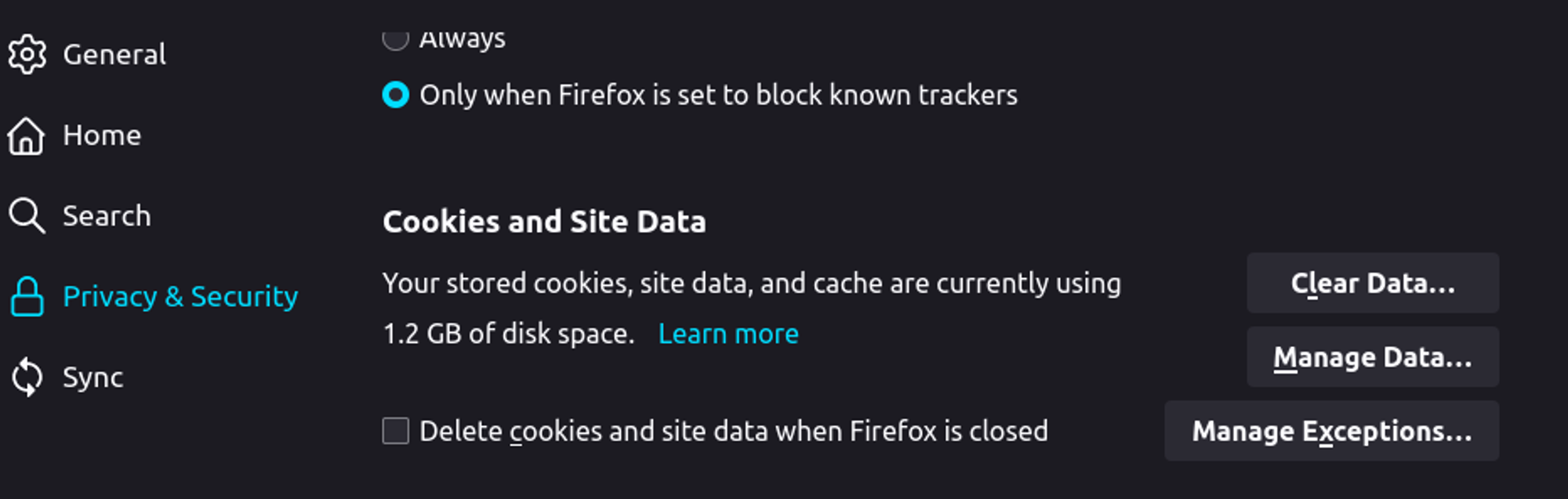
The desktop version of Firefox follows these steps:
- Click the three bars in the right-hand corner
- Choose “settings”
- Click “Privacy & Security” on the left-hand navigation menu
- Scroll down until you see the “Cookies & Site Data Menu.”
- Click “Clear data.”
To clear your history, you will need to scroll down a bit further until you see “Clear history.” Annoyingly, Firefox decided it was good to put these under two separate sections.
This screen also allows you to control your cookies and whether you want to keep any history. The “strict” advanced protection blocks most security, while a drop-down menu under the history section enables you to prevent all history tracking. Regardless, you will still need to clear your cookies.
Mobile (iOS and Android)
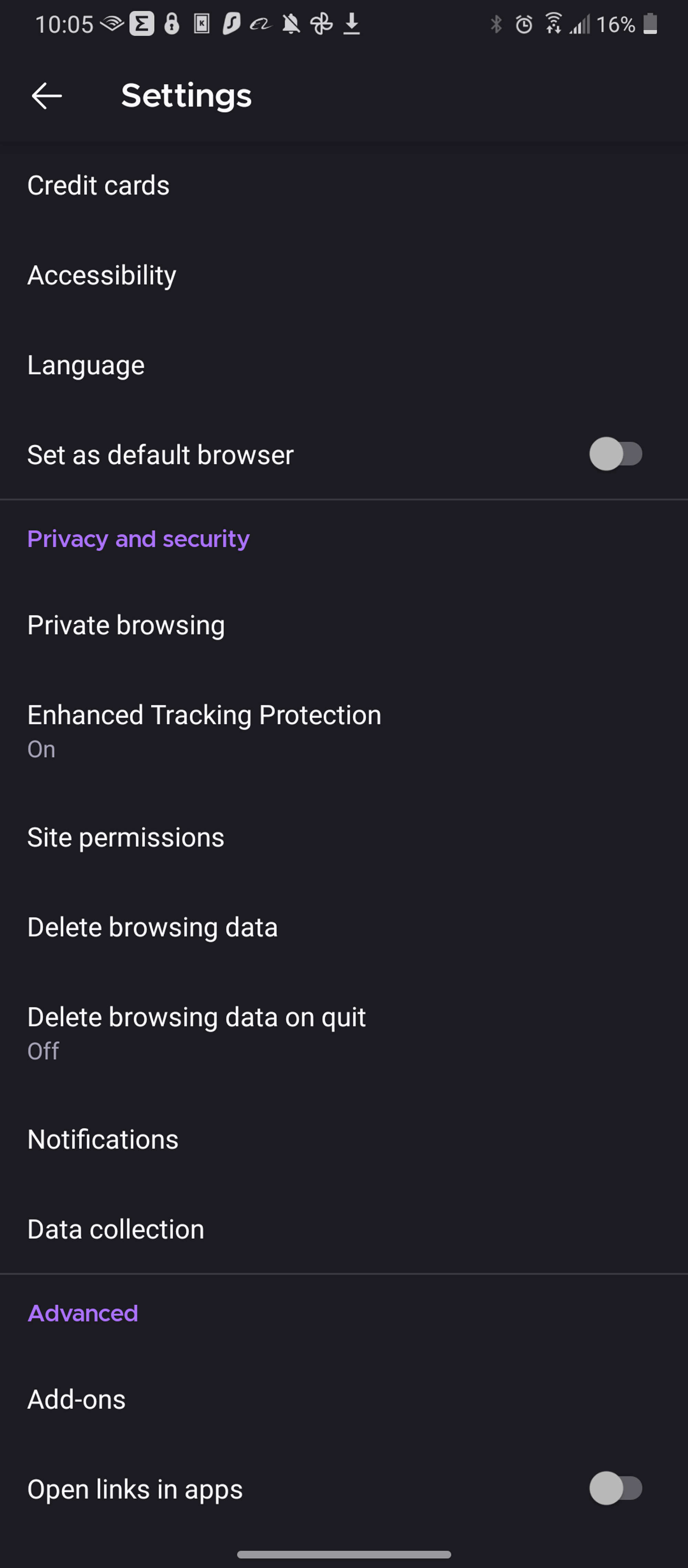
The mobile edition of Firefox tweaks your steps a little bit:
- Click the three dots in the bottom left-hand corner
- Scroll until you see “Delete browsing data” under “Privacy & Security.”
The mobile version deletes all browsing data, not just cookies, unlike the desktop version.
How To Clear Cookies on Opera
Opera is an odd duck in the browsing world because it has several iterations. Whether you use Opera GX (the gaming one) or Opera Mini, clearing cookies doesn’t change.
Desktop (Windows, Mac, ChromeOS, and Linux)
The desktop version of Opera takes a lot of cues from Chrome but is comparatively easier to spot:
- Click the settings bar in the upper corner
- Use the right navigation menu until you spot Privacy & Security
- Click the “clear” button next to browsing data
- Click “Clear browsing data” and the “clear data” button in the bottom-right corner
Much like Chrome, the “Cookies and other site data” header allows you to choose what cookies to block and whether you want automatic deletion after every use. However, Opera is not a privacy browser, as it does track your information.
Mobile (Android and iOS)
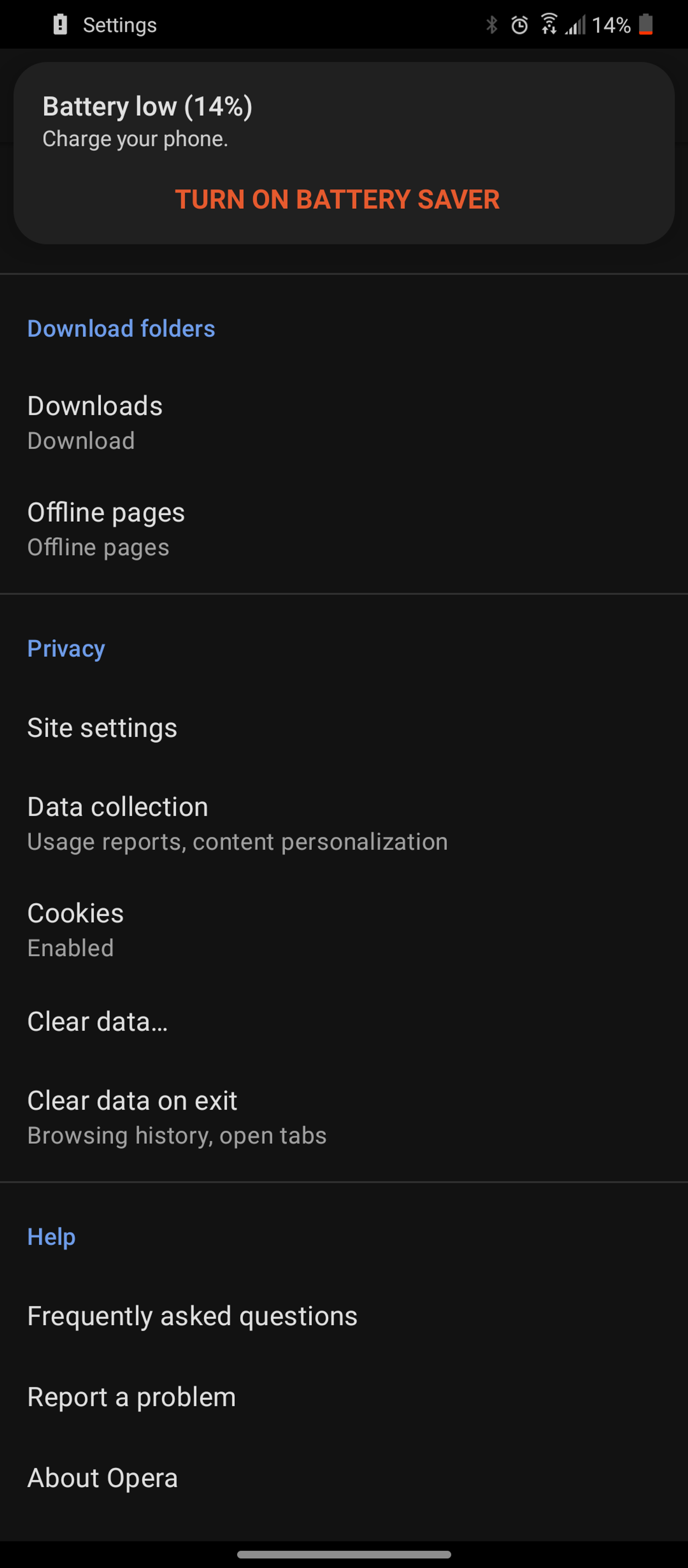
Opera’s mobile steps require a few more taps:
- Click your profile image in the bottom-right corner
- Tap the gear (settings)
- Scroll down until you see the “Privacy” heading
- Tap “clear data”
Clearing Cookies on Microsoft Edge
Microsoft is one of the larger companies known for data collection. Regardless, Edge is a drastic improvement over Internet Explorer.
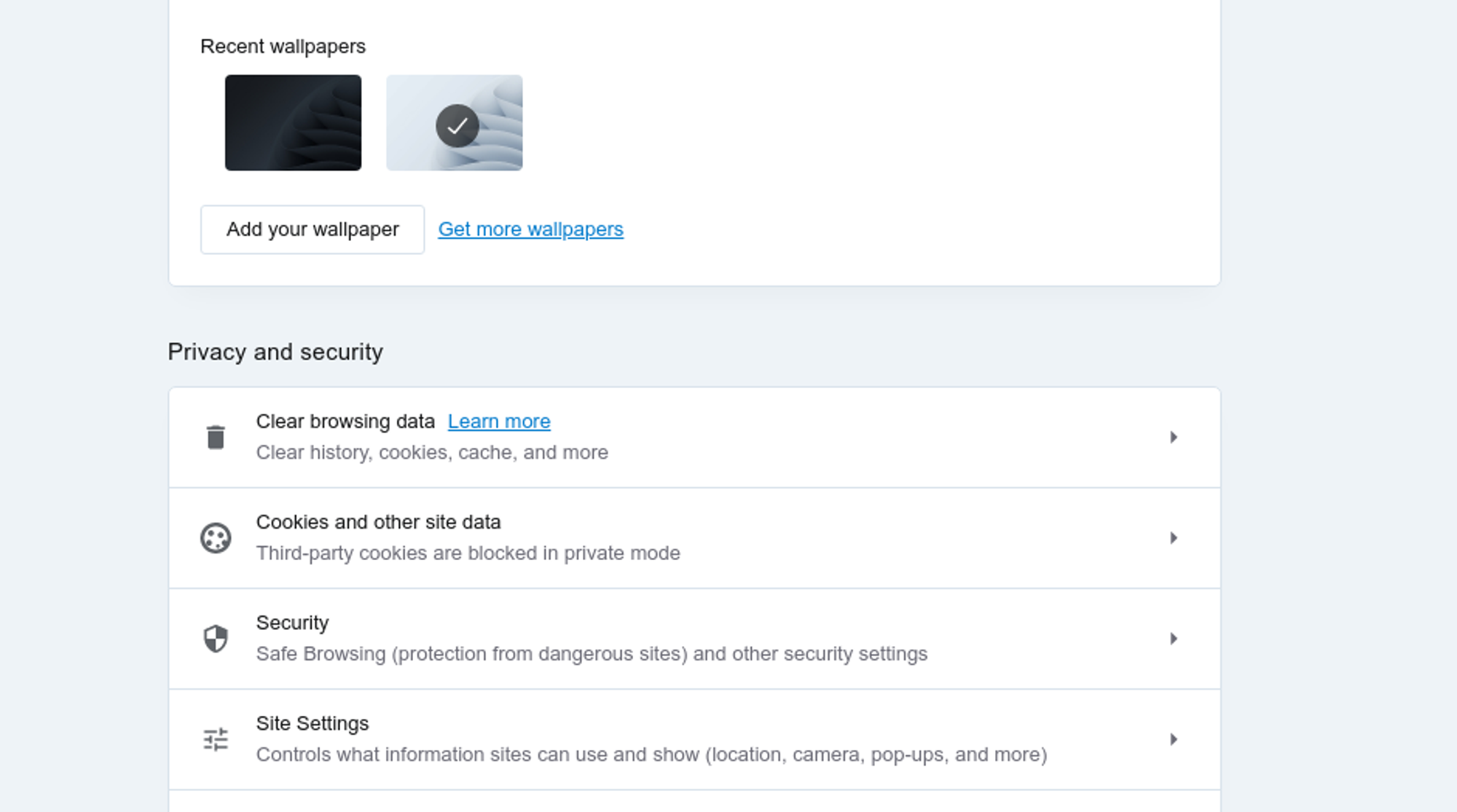
Desktop (Windows, Mac, and Linux)
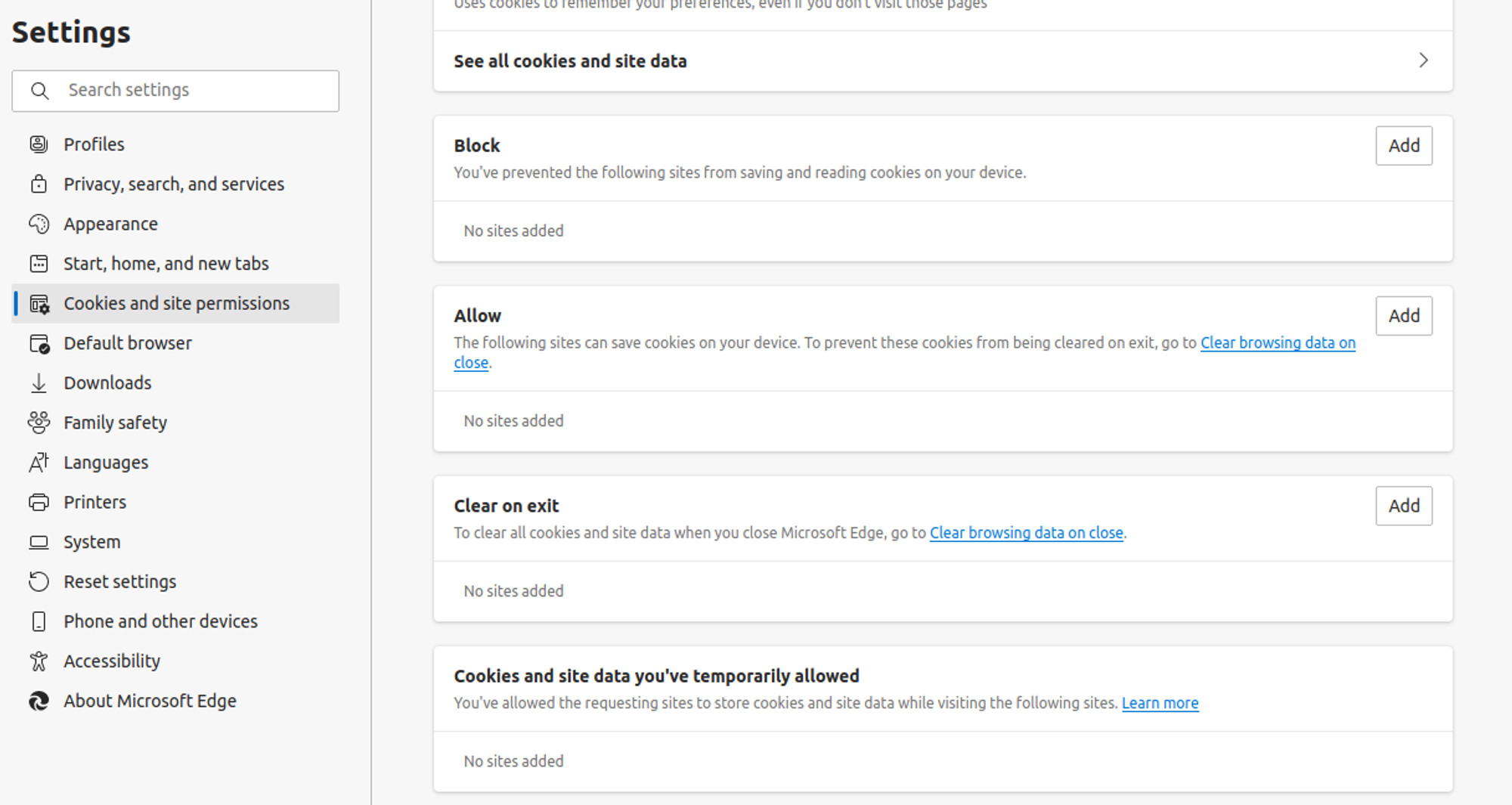
Edge is one of the more unintuitive experiences when it comes to clearing your desktop browser:
- Click on the three dots in the upper-right corner and click “settings.”
- Select “Cookies and site permissions” on the left-hand navigation menu
- Click “Manage and delete cookies and site data.”
- Select “See all cookies and site data.”
- Choose “Remove all” in the upper-right corner.
OR
- Select “Privacy, search, and services” on the left-hand navigation menu
- Scroll down until you see “Clear browsing data now.”
The first set of steps will only clear your cookies, not your browsing data. You can also set up strict tracking settings and automatically remove browsing data using the same screen.
Mobile (Android and iOS)
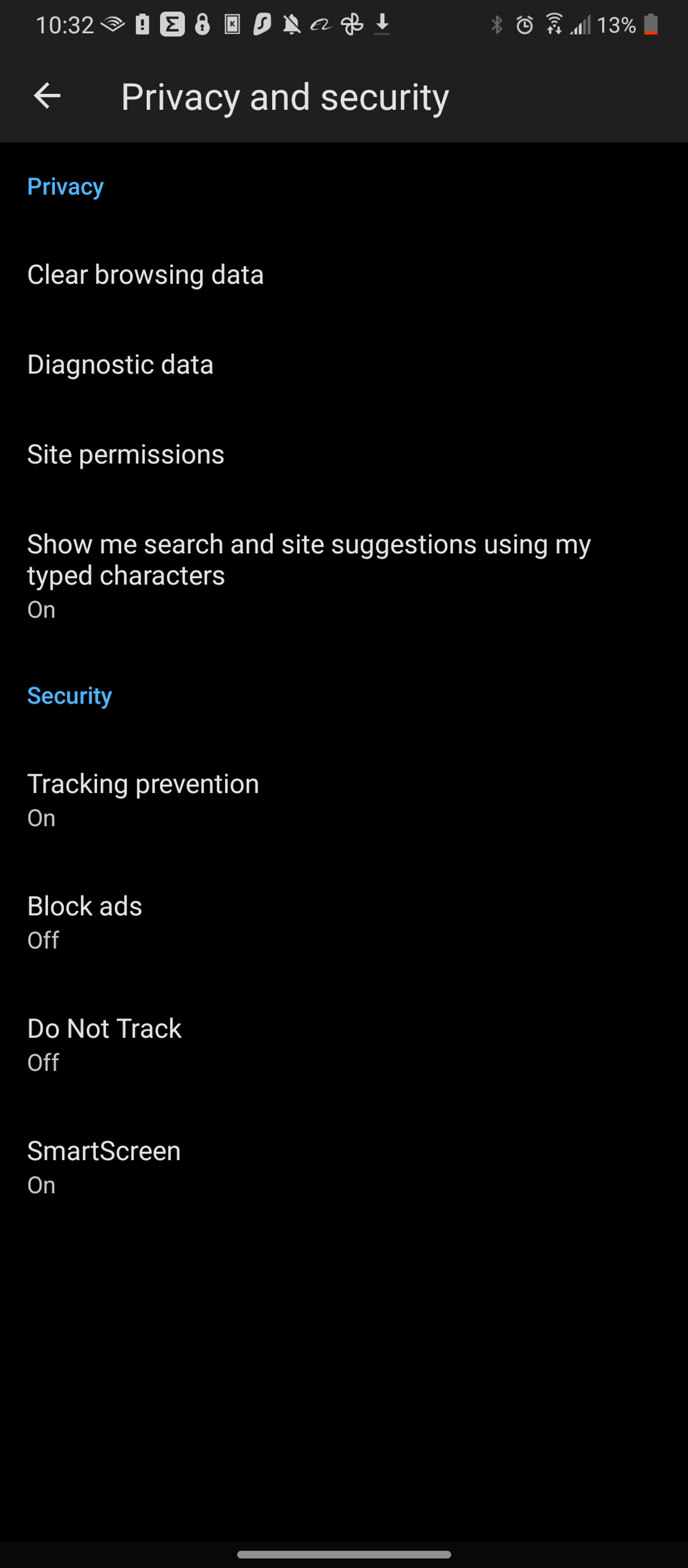
The only thing that changes with Edge’s mobile browser is the position of your options menu:
- Select the three dots in the middle-bottom section
- Choose “settings” on the far right
- Select “Privacy and security.”
- Choose “Clear browsing data”
Clearing Cache on Safari
Because Apple doesn’t like to share, these steps only apply to iOS and macOS. Safari discontinued support for Windows a few years ago. However, you can still get Safri on Windows if you have the tech skills.
If you are looking for a comparable Safari alternative, Opera is a good bet. However, neither of these are privacy browsers.
Desktop
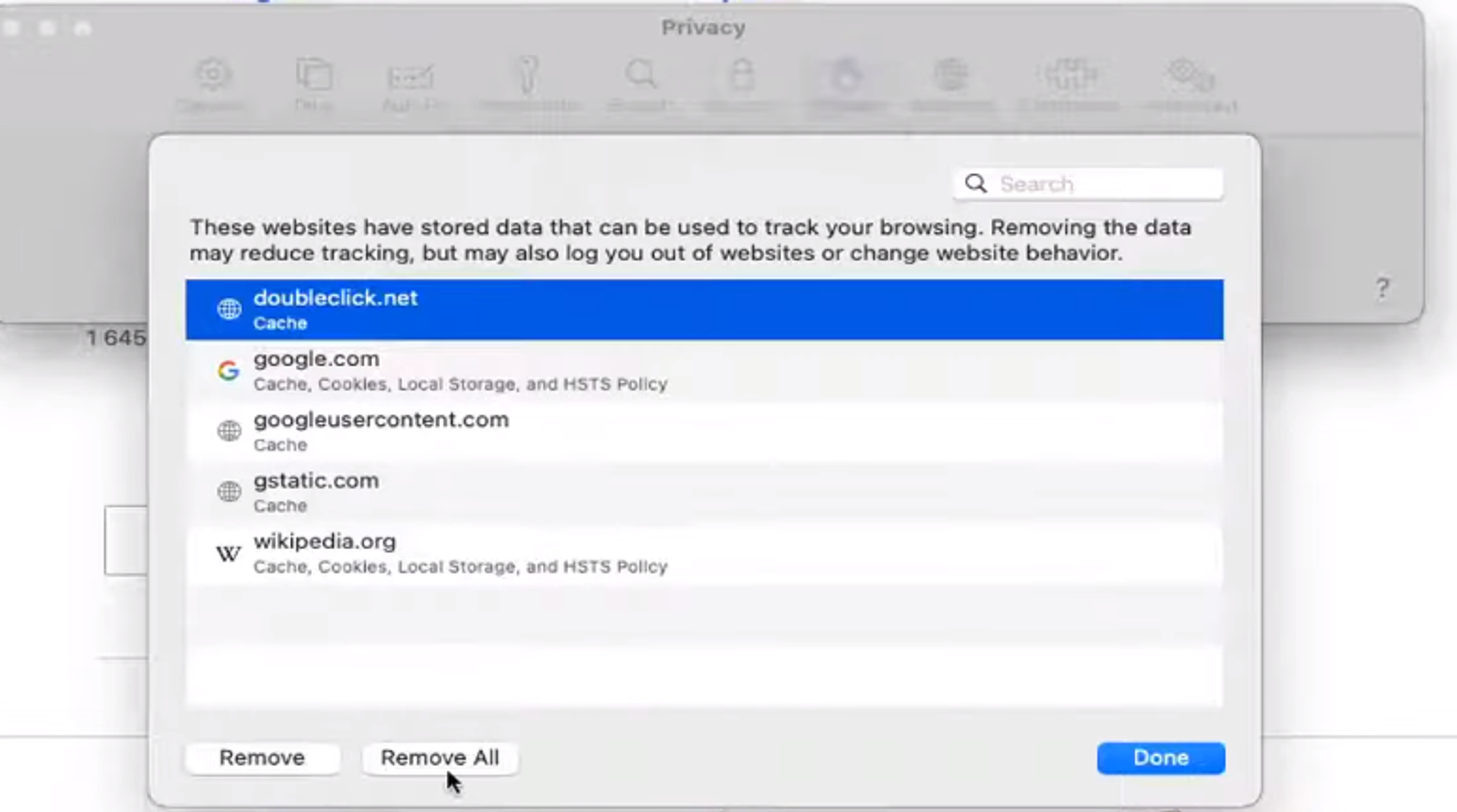
Because Apple has to be unique, you’ll find Safari’s browser clearing steps to be a bit different:
- Click on “Safari” in the top navigational menu on your Mac
- Choose “Preferences…”
- Select “Privacy” from the available tabs
- Choose “Manage Website Data…”
- Click “Remove All” on the bottom of the menu
Mobile
Unlike other Mobile devices, the typical way to clear internet data from Safari starts from outside of the browser:
- Tap on “Settings” from your phone’s navigation
- Tap “Safari” and scroll down
- Scroll to the bottom until you see “Advanced.”
- Tap “Remove All Website Data”
The general browsing data clearing request from outside the advanced tab will only remove some information. For a completely clean iPhone or iPad, you need to scroll to the very bottom.
While Apple isn’t quite as bad on the privacy front, they still store and use your data. Check out Apple’s Privacy Policy for details.
Deleting Cookies on Internet Explorer
To clear cookies on Internet Explorer, you can follow these steps:
- Click settings
- Select “general” and go to your browsing history
- Click “Delete…”
- Select Temporary Internet Files, website files, cookies, and website data from your checkboxes
- Click Delete
If you’ve still kept around Internet Explorer (for some reason), you’ve got a relic on your hands. While it might be entirely sensible for you to rush it to the museum, there are still honestly a few computers that exist with Internet Explorer on them. Nearly 5% of internet users still use the platform.
If you can, try and make the change to Linux in these cases. Linux is excellent for older computers, given its bare-bones focus. It also provides more security. You can also download a minimalist browser for further performance improvements.
Why Clear Cache and Cookies?
Your internet cache and your cookies cover a wide range of things. But the key comes back to privacy-conscious individuals keeping large corporations from tracking them.
Cookies contain a minimal amount of data. On sites like Facebook or Google, that data is more comprehensive.
This data can include location information. This information comes from the “site preferences” settings you set up from the beginning to allow location-based tracking.
Industrious hackers combine this information with connection and traffic logs to gather information about you. Eventually, they can use this information to hijack your accounts.
Clearing your cache also has the added benefit of removing unnecessary website data. Systems are constantly bogged down with cached data to make websites load faster. This situation doesn’t help if you don’t plan on returning to that site.
Will Cookies Affect My VPN?
Because cookies store account settings and preferences, they can impact your VPN. Old location-based data can eliminate the usefulness of cookies, preventing you from blocking location-based tracking. By clearing your cookies before using a VPN, you can avoid this.
Conclusion – How Important is Removing Cookies?
The removal of cookies is packaged alongside the deletion of search history and cached web content. While keeping these can improve your browsing experience, they expose you to certain risks.
Privacy-conscious individuals should always clear after each browser use. For further protection, activate your browser’s automatic cookie deletion feature.
For further protection, always use The Fast VPN’s data encryption features. They prevent traffic logs and connection logs from being combined with these cookies, providing you with the best protection online.
If your goal is to maintain online security, understanding networking basics is required. After all, letting someone get access to your home network is a significant security risk. But when you apply this to port forwarding, how does this apply to maintaining security?
Below, we will delve into this network security topic to understand how to use it. By the end of this article, you’ll know more about port forwarding, how to port forward, and whether it is safe for your network.
What is Port Forwarding?
Port forwarding (or port mapping) creates a direct and tunneled connection between a device on your LAN (Local Area Network) and another service on WAN (Wide Area Network, or Internet). It is a “tunnel” between your device and the desired service, sidestepping the router’s security. LAN involves all the devices connected to your home network’s router.
Typically, a router acts as a gateway between your network and the internet. Routers are a natural form of security but don’t always allow connections you want through. For example, routers will typically block connections coming from a game server.
When game servers see your connections blocked, you might have a strict or moderate NAT (Network Address Translation) type. Having a strict NAT type usually means that specific ports of the game you are playing are blocked.
Port forwarding tells the router that usually blocks these ports to open them up. This way, the game server that typically seeks these ports out has no impedance. This feature allows faster connection speeds, more reliability, and the ability to play with people regardless of their NAT type.
Is Port Forwarding Safe?
Overall, port forwarding is relatively safe when connecting your device to external servers. It is better than setting up an unregulated DMZ or disabling your router’s security. But there is a catch.
Having an open port on your router allows anyone knowing the port to access your home network. This port creates a wide-open door for anyone to waltz right through. All they need are two pieces of information:
- What game you are playing (this one is tricky)
- What ports your game commonly uses (this one is easy)
Remote criminals will also need your IP address, which is uncommon if you have a dynamic IP. But this won’t stop nearby people from plugging into your network.
The only exception to this rule is through Nintendo games. Nintendo recommends you open up ports 1 through 65535, making it more challenging to determine which port Nintendo uses.
This scenario is the homeowner’s equivalent to unlocking all of your doors and loudly announcing your unsecured house to all passing neighbors. In other words, don’t do this.
How to Port Forward on Your Router
Step One: Access Your Router’s Admin Page
If you want to start port forwarding, your first stop is your router’s admin page. The admin page is available on any router, but you must log in.
To log in, you need to find your gateway’s IP address, username, and password. You can find the gateway IP under your network & internet settings. The IP address you are looking for is the “default route.”
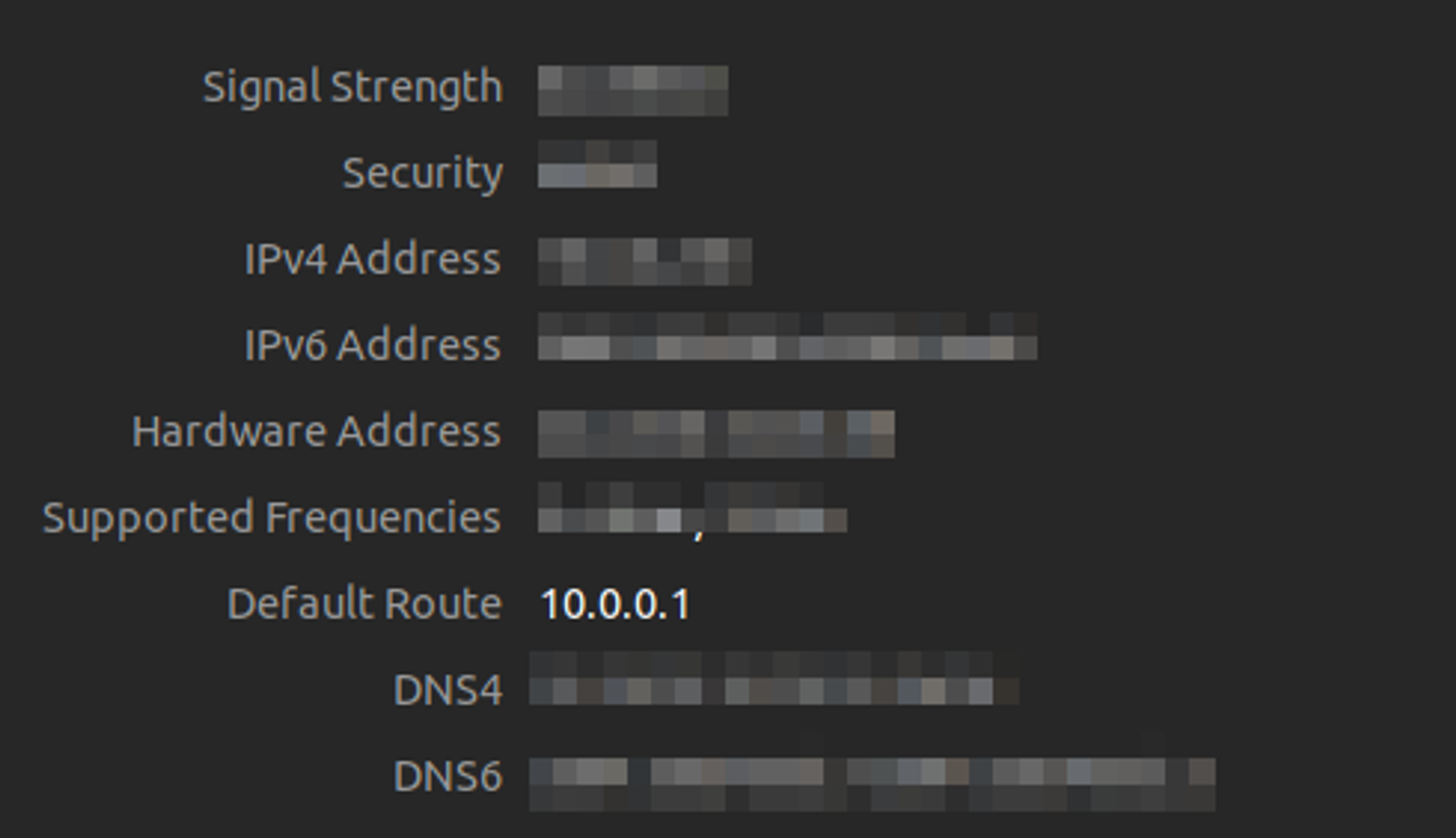
The default IP differs depending on your router. Typically, this varies by the company you use. If you struggle to find the information on your computer, you can also find it in your owner’s manual.
If you’ve lost your owner’s manual, your third option is to look on the side of the router. Typically, you will also find a username and password there that you need anyway.
If the side of your router doesn’t contain this information, look on the router company’s website. You’ll need to know your router’s model name and number. From plugging in this information on the company’s website, you should find what you are looking for. You can also use Google if you are desperate for answers.
Step Two: Getting To The Port Forwarding Page
Start by putting the default route IP into your favorite browser’s address bar. Once you’ve done that, your screen should resemble this:
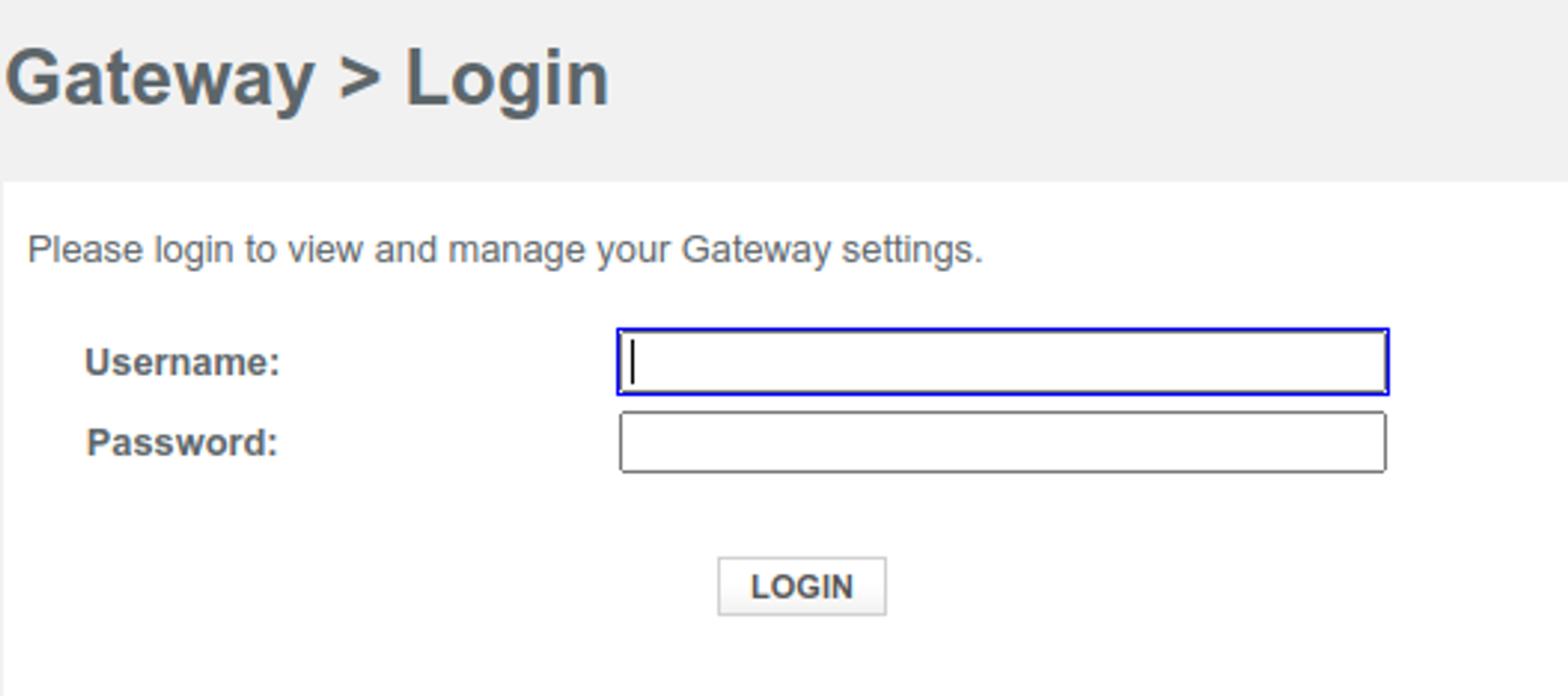
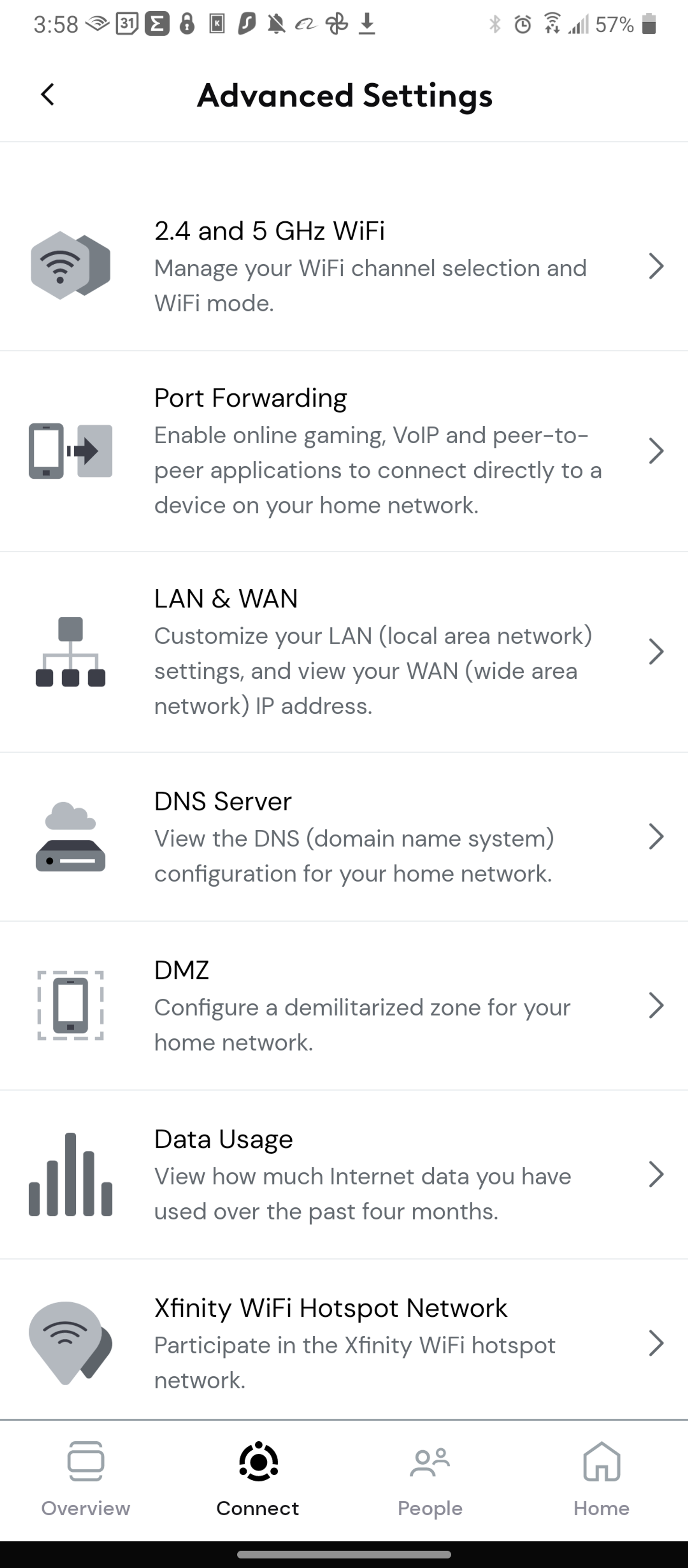
Input your username and password, and you should see a page that shows a variety of settings. Depending on your network provider, port forwarding is typically under advanced settings.
Some larger network providers also allow you to manage this through an app, like so:
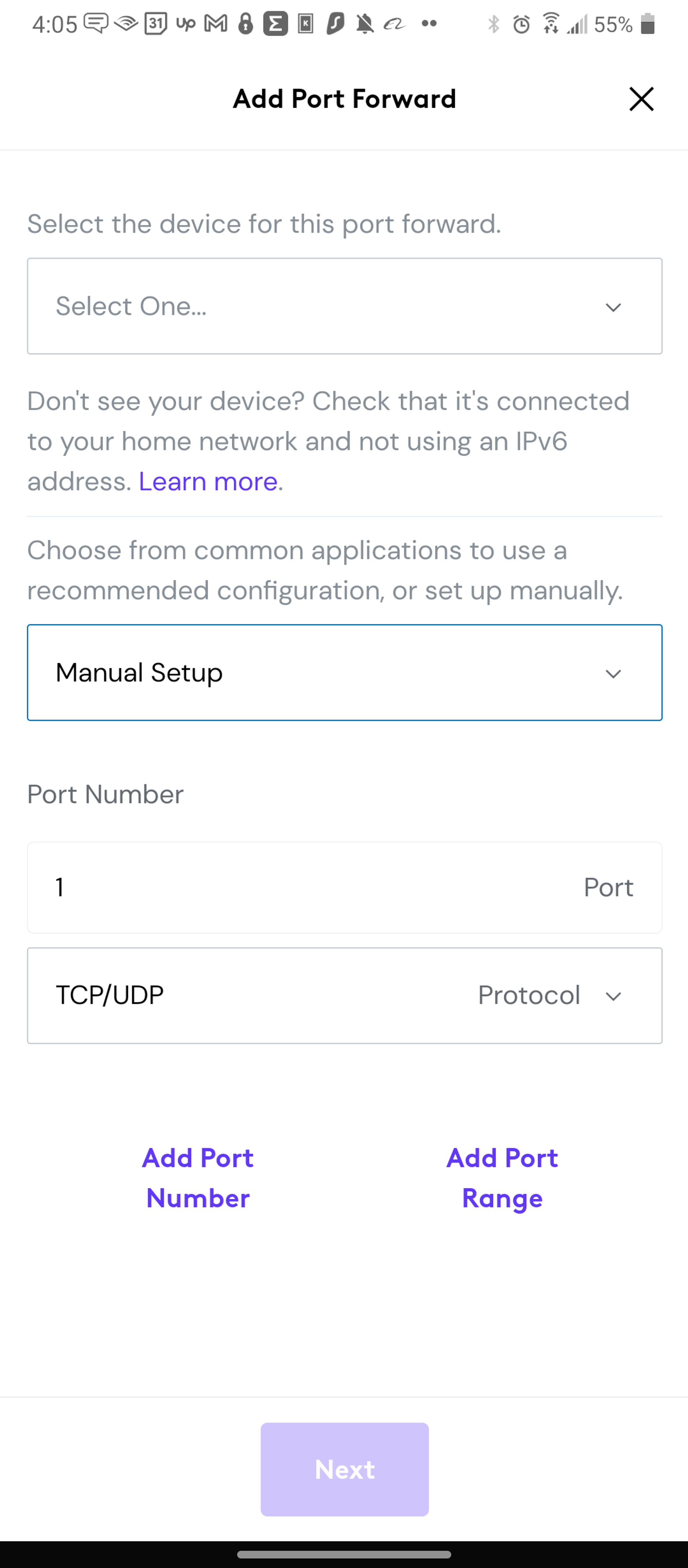
Tapping on port forward (or clicking on it) will bring you to a screen with existing port forwards. If you do not have any, you won’t see anything.
Clicking on the “add port forward” button will allow you to select two things:
- Device – Where the ports are forwarded from
- Port Number – The port number that you are going to input
- Protocol – Both TCP and UPD connection types
Step Three: Finding The Port Numbers
Once you’ve got to this page, it’s natural to wonder what to put in. Often, your internet service provider doesn’t provide this information; you have to find it.
Some ISPs are aware of this, enabling an “automatic setup.” This only inputs the default port number based on the ISP’s database of information. Because game servers sometimes go through updates, this doesn’t always work.
To supplement this information, you have a few options:
- Port Forward, the website which keeps an up-to-date database of ports.
- The company website behind the software you are port forwarding for.
- Random forums and a Google search.
Because all of these options have a chance to be wrong, you might have to go through all of them before you give up. In some cases, you will need to contact the customer service team of the software you are trying to forward. You might have to wait a bit, as they likely do not readily available this information.
Once you plug the port forward in and hit the “next” button, your port will be active. Test out your chosen software to see if it works and go from there.
What if The Port Gives Me an Error?
The most common reason port forwarding doesn’t work is existing ports. Typically, only one computer can have an open port at a time. So disable your current ports and try again.
Go back to your port forwarding dashboard and click the delete button next to the port to delete your ports. You might need to reset your router after deletion.
If you are still running into issues, try parallel ports that are one number up and one number down. When software companies update their ports, they typically do not go too far.
Sometimes, a blocked connection comes from a combination of a firewall and router. So in the event nothing works, check to see if your service needs a firewall exception.
Does Port Forwarding Work With a VPN?
Typically, port forwarding activities and VPNs do not work in tandem. With The Fast VPN, you’ll find this to be the case, so don’t bother using them simultaneously. Much of this comes from the inherent nature of the two activities.
Recall earlier that establishing ports for your preferred server is similar to creating a tunnel. VPNs, or Virtual Private Networks, establish similar tunnels to external servers.
Because VPN clients typically work on the device side, it is as if you are connecting a tunnel and building a brick wall. The encrypted data the tunnel finds is likely to cause connection errors.
Some VPNs (specifically PPTP and L2TP connections) use specific tunnels to exit. This tunnel enables those VPN types to connect through alternative ports. Many times, port forwarding only uses one port per device. Sometimes, this extends to one port per network, creating connection conflicts.
So, because the VPN server is already port forwarding, you cannot port-forward alongside another forwarded port.
Can You Port Forward on VPN Routers?
When using VPN routers, the situation stays the same. Because VPN routers connect to another data center to encrypt data through a forwarded port, it will cause a conflict.
Even if you could use your VPN router while port forwarding, any connection your device makes is an exposure. So port forwarding while utilizing a VPN eliminates the usefulness of your VPN
Where Do You Use Port Forwarding?
Despite port forwarding being a low-grade security risk, it does have its uses. Below is a shortlist:
Virtual Desktops
Modern desktops are often on cloud computing devices. This feature enables schools and businesses to save money while providing internet to stakeholders.
However, having connection slowdown and security blockages will cause issues. Port forwarding creates an open and secure connection between the two devices to address this.
Game Servers
Playing video games with your friends is great, but connecting to servers can be painful. Video games often require an unimpeded connection between you and the game’s server, reducing lag and communication issues.
Friends with different NAT types cannot always connect, resulting in poor game experiences. Forwarding ports enable you to stick with the preferrable moderate (or open) NAT types for gaming.
Remote Access and Backups
Direct communication between your computer and another can sometimes be necessary. When accessing a remote desktop or server, overcoming security is occasionally challenging.
Regular and straightforward access to backup data is often through port forwarding. This backup information is given easier access behind other security measures.
CCTV and Security
CCTV camera feeds have direct connections to security company’s monitoring services. If you’ve received a motion alert on your phone from a security system catching a raccoon, you know how this feels.
In the case of security, closed-circuit systems also exist as a form. But in cases where multiple computers and a network are involved, a port forward can simplify your connection and improve response time.
Types of Port Forwarding
With the different uses for port forwarding, there are different types. Here are three significant types of forwarding you might be familiar with:
Local Port Forwarding
Local port forwarding refers to connecting your local network computer to an external server. This process usually involves putting specific port information on your local firewall.
This forward comes from an application on the same computer, handled through an SSH (Secure Shell) client. The client listens for incoming connections and decrypts the data on your behalf. An excellent example of this in action is an inter-company email server.
It is the most common form of port forwarding because it involves requesting consent from both sides. If you are trying to play games with friends, the game server already has this open for you. Inserting the game ports from their company website ports opens your computer up for them.
Remote Port Forwarding
Remote port forwarding is very much the opposite of local port forwarding. It refers to server-side applications offering a secure connection through their ports.
Remote port forwarding often involves allowing other computers to access backups or remote servers. While you still need to know some credentials to get in, the server handles the connection.
Dynamic Port Forwarding
Dynamic Port Forwarding (DPF) uses firewall pinholes for direct connections. This port forwarding type is typical when you connect to a trusted third-party server.
The server then connects to a series of other services on the other side. DPF is often applicable when you need an extra layer of security, such as a SOCKS Proxy Server.
As a result, DPF tools are helpful when protecting yourself on public servers. However, many of these proxy servers do not encrypt your data, giving them weaker security measures.
Port Forwarding Benefits
Knowing everything about port forwarding, there are some pretty substantial benefits to setting it up:
- Faster connection speeds. Having an open port between you and your target service provides speedier loading times. This more incredible speed can be great for inbound traffic and online gaming.
- Great way to access essential documents. Need easy access to critical documents from everywhere? Port forwarding provides that instantaneously from any location.
- Maintains security elsewhere. Having a single open port is the safest method of opening your router. There is no impact on other security aspects of your router.
- Can host online games and servers. Port forwarding is helpful if you want to host a server for an online game. Having a single open port gives people a simple pathway to travel through.
Port Forwarding Risks
Often, you end up trading convenience for security (and vice versa). Below is how port forwarding can be risky.
- It gives users unlimited access. Anyone who knows about this exposed port has complete access to whatever tools you use it for. This can include access to sensitive data and your remote PC.
- Can expose your IP. If you use a VPN and are concerned about privacy, port forwarding can ruin that. The wrong user can find your IP and location using this exposed point.
There are two ways to prevent port forwarding risks: First, you can choose to require online credentials for users accessing the data. If users want to access it, they will need another authenticator you give them.
The second method for preventing hackers from accessing port forwards is closing the port. When you are done, closing the port re-activates the security.
You can also keep up your firewall, which often blocks unwanted connections regardless. However, some applications (primarily games) have the same port limitation issues with firewalls.
Port Forwarding FAQs
What is TCP?
TCP, or Transmission Control Protocol, allows application programs and computers to communicate. It is a primary communications standard of the internet, guaranteeing the integrity of data sent. Because of the focus on data integrity, TCP is slower than its similar cousin: UDP.
Together, TCP/IP is the preferred way of communicating online. This enables people to identify different connections, allowing for a straightforward definition of where you send your data.
What is UDP?
UDP, or User Datagram Protocol, is a fast protocol commonly used for video and voice traffic. Its speed comes from its tendency to send data before a formally established connection.
Because of this habit, the protocol sends entire data packets with built-in headers, requiring quick authentication of the two users. The chance of data loss is a bit higher, as a result, making it suitable for non-essential data sending and communication.
What is NAT?
NAT, or Network Address Translation, transforms multiple local IP addresses into a single public IP address. The public IP address is that of the router, seen in IPv6.
Combined with the port types above, you can identify where the computer comes from by looking at your router diagnostics. So instead of revealing your private IP address, you find the named device using a specific port.
Depending on whether a specific application port is open, different NAT types apply. For example, a moderate NAT is most likely the case when using port forwarding.
Conclusion – Should I Trust Port Forwarding?
In the grand scheme of things, port forwarding is perfect. Much like VPNs, it provides a secure tunnel between you, your app, and your target device. While the risks for leaving a port open are relatively high, having a client-facing firewall often solves this problem. By establishing a reminder to close the port when finished, you solve many of the most challenging issues with port forwarding.
For an alternate method on internet security, download The Fast VPN. While port forwards and VPNs do not always get along, having multiple security options provides you with more excellent protection.